Today, Red Hat has issued an urgent security alert for Fedora Linux 40, Fedora Linux 41, and Fedora Rawhide users concerning a security flaw (CVE-2024-3094) found within the XZ Utils 5.6.0 and 5.6.1 packages. This flaw could potentially allow unauthorized remote access via SSH.
It appears that the upstream tarballs of the XZ Utils 5.6.0 package, shared via GitHub or the project’s official website, included additional .m4 files with instructions of building the software with a GNU Automake version missing in the repository.
During the liblzma library compilation, a prebuilt object file, extracted from one of the test archives, is used to modify certain functions within the XZ Utils’ code. Since software like sshd utilizes the liblzma library, malicious actors could use it to gain remote access to a compromised system.
“The resulting malicious build interferes with authentication in sshd via systemd,” the security advisory reads, “Under specific conditions, this interference could potentially enable a malicious actor to bypass sshd authentication and gain unauthorized remote access to the entire system.”
Red Hat warns users of Fedora Linux 40 beta, Fedora Linux 41 (pre-alpha), and Fedora Rawhide users to stop using their systems for business or personal use. Fedora Linux 41 and Fedora Rawhide systems already include the affected XZ packages, but it also looks like these were supplied to Fedora Linux 40 beta users earlier today.
For Fedora Linux 40 beta users, there’s an update that reverts the XZ package to version 5.4.x and it should become available to users through the normal update system. To force the update, you should run the command below in a terminal emulator or follow the instructions from here.
sudo dnf upgrade –refresh –advisory=FEDORA-2024-d02c7bb266
While Fedora users may be affected, Red Hat states that this security flaw does not affect any of the Red Hat Enterprise Linux releases. Other GNU/Linux distributions that ship with XZ Utils 5.6.0 or later versions should be affected as well. However, none of the known stable distros include these newer XZ Utils versions.
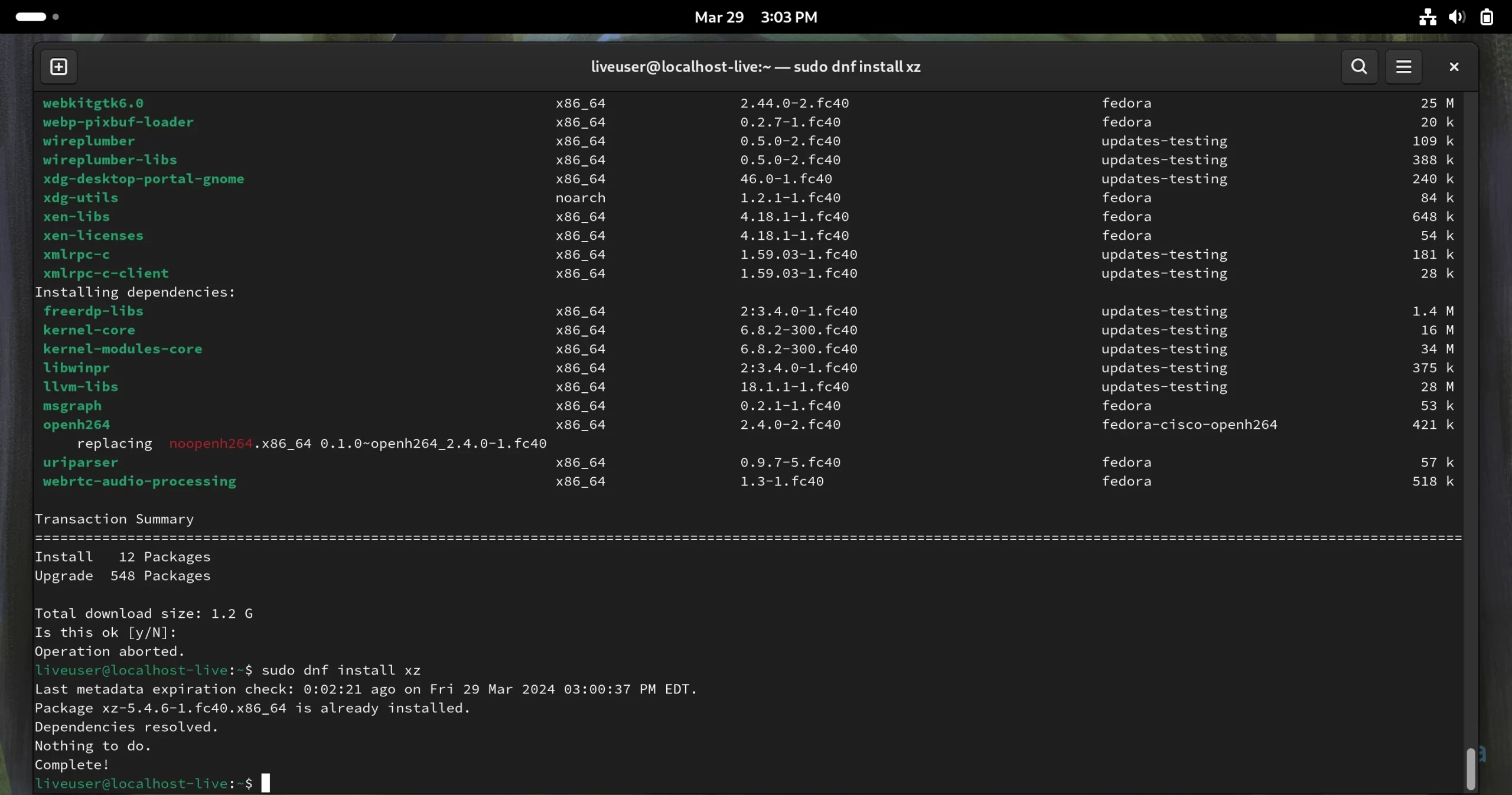
In good news for Fedora Linux 40 beta users, the live ISO images come with XZ 5.4.6, which is immune to this issue. Albeit, the not-so-good news is that if you update your installation, the newer XZ 5.6.0 update could be installed automatically. Therefore, Please do not update your installations if you’re using XZ 5.4.6.
If you’ve installed XZ 5.6.0 (check with <a href="sudo dnf install xz rel="nofollow" target="_blank">), the command previously mentioned is now functional for Fedora Linux 40 beta systems and it’ll downgrade the package version to 5.4.6 while removing version 5.6.0 from your system. As of this writing, XZ 5.6.0 is no longer offered as an update to Fedora Linux 40 beta users.
This vulnerability only impacts 64-bit (x86_64) systems. Furthermore, it only becomes exploitable if your SSH daemon (sshd) is accessible from the Internet.
Andres Freund provides a detailed analysis here of how this vulnerability affects your system after testing on Debian Sid (Unstable). Red Hat indicated that openSUSE distribution users are also affected, and SUSE has published a downgrade procedure here for users who have installed the vulnerable XZ package.
Between March 26th and March 29th, Kali Linux users were impacted by this vulnerability. Offensive Security now advises Kali Linux users to update their installations immediately to implement the most recent patches if their systems were updated on or after March 26th.
Vegard Nossum has now created a script that checks if your ssh binary is vulnerable. You can download it from here and run it using the sh detect_sh.bin command in a terminal window.
The openSUSE Project published a statement addressing the recently discovered vulnerability in the XZ compression library. This issue impacted the openSUSE Tumbleweed and openSUSE MicroOS distributions. As outlined in the statement, from March 7th to March 28th, users of these distributions had the affected XZ 5.6.1 package loaded in their systems. This was rectified by the openSUSE Project through a rollback to XZ 5.4.
Richard W.M. Jones, a computer programmer at Red Hat, indicates the individual responsible for the backdoor had been a member of the XZ Utils project for a two-year duration, contributing numerous binary test files. Jones had been in talks with him over several weeks, attempting to add XZ 5.6.x to Fedora Linux 40 and Fedora Linux 41, citing its “excellent new features”.
There was also an advisory about security from the Arch Linux developers, who stated that for their version of sshd, “the harmful code path does not exist, as it does not link to liblzma”. It is recommended for Arch Linux users to upgrade to xz 5.6.1-2 to prevent the defective code from being present in their systems, as it may be activated from other, unidentified directions.
As of 5:40 pm ET on March 29th, 2024, the information presented in this article is accurate. I’ll update this blog post if there will be updates to this situation.
Last updated 17 seconds ago